Decrypt Dmg File Without Key
Are you trying to open some files on your computer that are encrypted? Windows will usually designate encrypted file or folder names with the color green instead of the normal black text.
After the encryption it will rename the files as a HTML file, with inside the original encrypted file. If you try to open any of these encrypted files, you will be redirect to the malcious web page, which is currently at xblblock.com, that will display the same screen of the “Decrypt Protect MBL Advisory” and will try to persuade you to pay the ransom in the form of a MoneyPak voucher. 7-Zip is a free open source DMG extractor software for Windows. It is a popular file.
Xda-developers Android Development and Hacking Android Apps and Games Decrypting WhatsApp crypt12 files by TripCode. Android Apps and Games; Android General. Just trying to decrypt the file. There is a program out there which claims to obtain the key file without root. If it's still working today, I don't know. Sep 10, 2012 how to open a.dmg or.pkg without a password Mrtechdudel01. Unsubscribe from Mrtechdudel01? Cancel Unsubscribe. Subscribe Subscribed Unsubscribe 20. That big one is the (encrypted) filesystem (i.e. The one that is installed on the device). If you use iDecryptIt on the file, iDecryptIt will decrypt it. The decrypted file can then be extracted with (the included) 7-Zip or mounted as a virtual hard drive with certain tools. Please do not contact me asking for keys. Open macOS DMG files on Windows. Extract any file from a DMG archive with just a few clicks! Open macOS DMG files on Windows. Extract any file from a DMG archive with just a few clicks! IPhone Backup Extractor BlackBerry Backup Extractor DMG Extractor Reincubate Lookup.
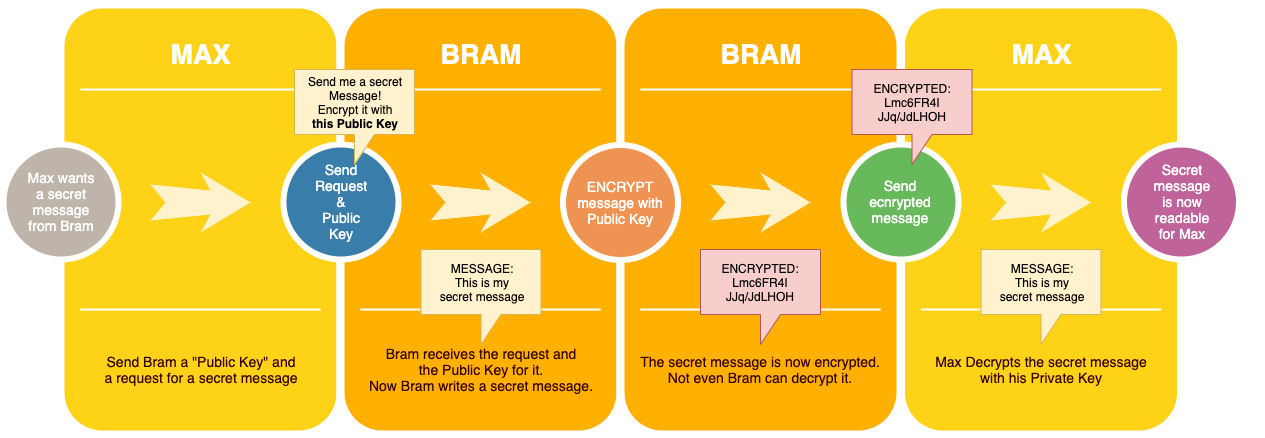
The key used to encrypt the files is derived by a key derivation function (HMAC-SHA1) as follows: encryptionKey = HMAC-SHA1(hashplaintextfile,user chosen master password). With this key the user allows someone to decrypt a specific file, without the need to. According to the website HFSExplorer can open and read encrypted dmg images. HFSExplorer is an application that can read Mac-formatted hard disks and disk images. It can read the file systems HFS (Mac OS Standard), HFS+ (Mac OS Extended) and HFSX (Mac OS Extended with case sensitive file names). Cracking encrypted disk image, AKA DMG is feasible, but, and there are many buts, is extremely, extremely time consuming. If you do not remember at all the password, or if you attempt to crack in 'blind mode', you will probably need to teach your kids how to do it: By the time you'll have a fighting chance, you'll be long dead.
Note: If you are reading this post looking for information on decrypting files that were encrypted by CryptoLocker, this won’t help. You pretty much have to pay the ransom and hope they actually send you the encryption keys.
When encrypting files and folders, Windows will use a self-generated certificate that contains keys used to encrypt and decrypt the data. When opening encrypted data when logged into the user account that generated the certificate, the decryption process is transparent and the files are opened normally.
However, if another user or system tries to access those same data files or if the files are moved to another location, then they cannot be opened unless the original certificate is installed.
Maybe you like Cataclysm content but not the terrible talents, changes and etc? You could bring Cata to 3.3.5.Then there are a lot of technical benefits, especially for Nostalrius, that I talked about towards the end that allow you more opportunities to scale. Like quest linking in chat for Vanilla WoW. Hack dmg wow 3.3 5a. Lots of features that don't kill the game that are missing from the 1.12.1 client.You could come up with more radical things like backporting an entire expansion's worth of content to 3.3.5.
IDecrypt is a GUI front-end for VFDecrypt (resulting in this program breaking GNU GPL) for Windows/OS X. It's used to decrypt.DMG files, namely the rootfs of an IPSW file. The tool is very simple to use. Here are the Steps: Select file to decrypt; Enter key if not found automatically - Get them from this wiki; Chose output folder; Click.
In either case, one thing you have to remember about encrypting and decrypting files in Windows is that you always need the encryption certificates/keys. When you encrypt a file or folder in Windows, encryption keys are automatically created and associated with your user account.
In Windows 7 and higher, you’ll actually get a prompt asking you to backup your encryption key (EFS certificate).
You should definitely do this immediately. If you do not have these encryption keys, you will not be able to decrypt the data. Unfortunately, there is no way around this since the encryption is very strong and cannot be broken easily.
If you can still access the computer where the data was originally encrypted, you can try exporting the certificate and then importing it on a different machine.
Backing Up EFS Certificates
There are a couple of ways to backup file encryption certificates and I’ll mention them below. The first way is to click on Start and type in certificate.
Oct 09, 2015 Sylenth1 is a virtual analog synthesizer that takes the definitions of quality and performance to a higher level. Until now only very few software synthesizers have been able to stand up to the sound quality standards of hardware synths. Sylenth1 is one that does. Sylenth1 is not just another synth. It was built from a producer's point of view. Sylenth1 mac download. Sylenth1 Demo Download the latest Sylenth1 demo version here: Windows 32/64-bit v3.055. MacOS 32/64-bit v3.056. Limitations of the demo version: A demo reminder sample will be heard about every 60 seconds. Half of the modulation options have been disabled.
Click on Manage user certificates and this will open up the certificates for the current user. In Windows 7, you can also type in certmgr.msc and press Enter to open the certificate manger.
Now expand Personal and then click on Certificates. You should see all the certificates listed in the right pane. There might only be one, but if not, the only certificates you are interested in are the ones that have Encrypting File System listed under Intended Purposes.
Right-click on the certificate, choose All Tasks and then click on Export.
This will open the Certificate Export Wizard, which is the same place you will reach if you click on Back up now (recommended) when prompted by Windows.
On the next screen, you will want to select Yes, export the private key along with the certificate. If you don’t have the private key, you won’t be able to decrypt any of the encrypted files.
On the next screen, you have to choose the format you want to use to export the certificate. Personal Information Exchange should already be selected and you can leave it with just the first box checked.
Since this certificate contains a private key, you are required to protect it using a password. Check the Password box and type in a strong password.

Finally, click Browse and choose a location where you want to save the file. It is highly recommended you do not save the file onto the computer itself. If something happens to the PC, then you lose the key along with it.
Also, give your file a name that is helpful for you, but not super obvious to others what it is. For example, don’t name it EFS key like I did below!
Click next and then click Finish. Your private encryption key is now saved as a file. You can now take this file and import it on any other Windows machine. Importing is really easy. All you have to do is double-click on the file and it will open up the Certificate Import Wizard.
Once you import the certificate, you will be able to decrypt any files that were encrypted with that certificate. As previously mentioned, if you are trying to open encrypted files and you don’t have or can’t find the certificate anymore, then those files are basically gone.
Some programs state they can decrypt your files for a hefty price, but they have never worked for me and that’s why I haven’t listed any of them here. If you have any questions, feel free to post a comment. Enjoy!
Original source: https://github.com/0xced/iOS-Artwork-Extractor/wiki/Extracting-more-artwork
You can extract even more artwork if you decrypt and mount an iOS firmware (.ipsw file).
Requirements
- Python 3.2 (required by ipsw_decrypt.py)
- VFDecrypt (required by ipsw_decrypt.py)
Make sure to install thevfdecryptbinary somewhere in your PATH or use the-doption of the theipsw_decrypt.pyscript.
VFDecrypt Usage:
How to decrypt and mount an iOS firmware
- Download an iPhone or iPad firmware that matches your simulator version and make sure that there is a VFDecrypt Key by checking the corresponding Build column. For beta versions, check the VFDecrypt Keys page instead.
System Firmware Image ipsw
Decrypt Dmg File Without Key
| Version | Build | Codename | Baseband | Release Date | IPSW Download URL | SHA1 Hash | File Size |
|---|---|---|---|---|---|---|---|
| 9.0 | 13A343 | Monarch | 1.00.05 | 16 Sep 2015 | iPhone8,2_9.0_13A343_Restore.ipsw | 62c84322d95913ddcee8337c0998988c6acd330e | 2,369,374,167 |
| 9.0.1 | 13A405 | Monarch | 1.00.05 | 24 Sep 2015 | iPhone8,2_9.0.1_13A405_Restore.ipsw | c13f78d5967632732841fcae9840bfd37d09b5af | 2,368,629,853 |
| 9.0.2 | 13A452 | Monarch | 1.02.00 | 30 Sep 2015 | iPhone8,2_9.0.2_13A452_Restore.ipsw | 46b922b4755fcb66e9f33dd491002e120b88908a | 2,369,099,889 |
| 9.1 | 13B143 | Boulder | 1.14.00 | 21 Oct 2015 | iPhone8,2_9.1_13B143_Restore.ipsw | 634807da8e723d688419b56f14b0913aee317760 | 2,383,904,492 |
| 9.2 | 13C75 | Castlerock | 1.23.00 | 8 Dec 2015 | iPhone8,2_9.2_13C75_Restore.ipsw | f89ea6f273dde92167c408decdb5db3daa756a19 | 2,382,945,535 |
Backup Firmware Image
- Start iTunes on your computer, and then connect your iPhone to your computer using its sync cable.
- Click the button for your device near the upper-right corner of the iTunes screen, and then click the 'Summary' tab if it isn't already selected.
- Select 'This Computer' in the Backups section, and then click 'Back Up Now.' ITunes backs up your entire iPhone, including iOS, to the hard drive.
- Confirm that the backup was successful by selecting 'Preferences' from the main iTunes menu, clicking the 'Devices' tab, and then making sure that the time and date next to your iPhone's entry correspond to when you finished the backup.
- Disconnect your iPhone from your computer.
Decrypting with ipsw_decrypt.py
Dmg File Mac
Run the
ipsw_decrypt.pyscript on the firmware you downloaded or backed up.The output should look like this:
Go into the
iPhone 4, 5.1 (9B176)folder or whatever folder was created depending on the firmware you chose.Open the biggest file ending with
.decrypted.dmgin order to mount the disk image. In this example:038-1768-165.decrypted.dmgRun iOS Artwork Extractor. If the mounted iOS firmware version matches your simulator version, then you will discover much more artwork.
iOS 8 firmware
Decrypt Any File
Decrypt Dmg File Without Keys
VFDecrypt Keys are not widely available for iOS 8. You will have to use vfdecrypt directly on the unzipped iPhone 4S ipsw with the key provided by @iH8sn0w:
Decrypt Dmg File Without Key Download
Decrypt Dmg File Without Key Download
@Jato_BZ which keys? Or just rootfs like the 4S one? 5059b2da95c93f754ce4a701cf6564877dfee899ad884d78f3403dcec7bbd6fe6d3079a8